Integrated Enterprise Infrastructure Solutions
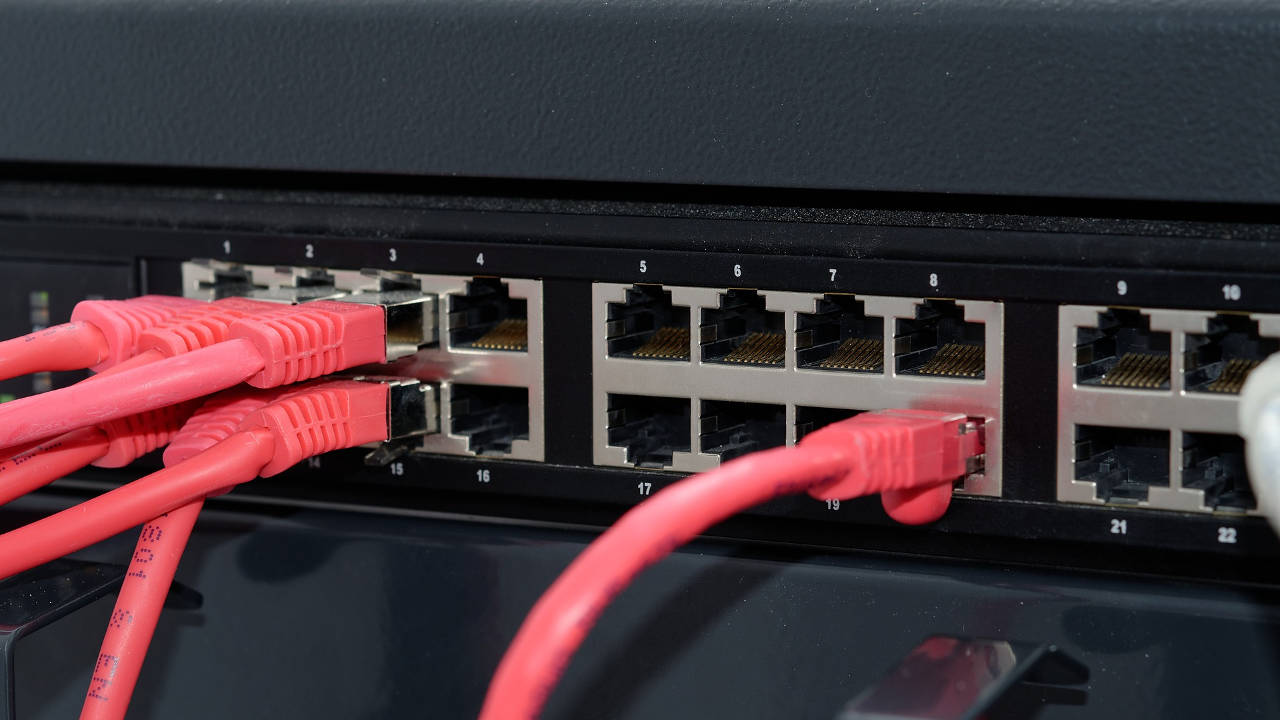
Computer networks have become the heartbeat of the technologically connected world and are indispensable to business and daily life. Because of this they have also become a target for criminals. Overall complexity of networks, applications, and security has been advancing at a staggering rate with threats, security tools, and countermeasures becoming ever more sophisticated. Many businesses, especially small ones, struggle with obtaining the skills required, and even if they can find the people, cannot justify the costs associated with a specialized IT staff.
Jade Networks helps companies with the design, implementation, deployment, management and outsourcing of enterprise networks. We also help in areas including disaster planning and recovery, policy planning and analysis, network and vulnerability assessment, network automation, and others. Our managed services are described in our Overview to Managed Services page and in detail in the Security, Monitoring, and Analysis/Response Systems sections below. All these areas are closely related to each other and are treated separately for descriptive purposes only. We also provide hosting and consulting services. Let us know if you have any questions and we'll be happy to get right back to you.
Security
Security is one of our top priorities in the management of our networks and customer managed services. Security of all types (physical, network, application, operating systems, and social engineering threats) must be properly managed. A breach in any of these areas is all that is needed to put an organization at risk.
more...
Monitoring
Monitoring systems actively collect, store, analyze, display and act upon data related to enterprise networks. This information is used not only for the daily administration of a network but for many other purposes, including performance and fault analysis, capacity planning, and more.
more...
Analysis and Response Systems
Collecting operational data is great but the real power of these systems is their ability to analyze the data to detect, alert, and resolve anomalies. The ability to analyze and react to problems is found in many products ranging from security, monitoring, SIEM, applications and custom built tools.
more...
Services and Network Operations
Hosting Services
The following Internet hosting services are provided: Domain Name (DNS), Electronic Mail, Web, VoIP, and dedicated servers. Additional services can be provided upon request. All Jade servers are RAID configured with automated backups done to redundant backup servers several times daily.
more...
Network Operations
The Jade Network is a /22 IPv4 network located in Kowloon Bay, Hong Kong. The network is tightly managed and monitored using many of the same tools we apply to customer networks. We have also developed our own security infrastructure which co-exists with other standard security solutions.
more...
Consulting
We provide consulting services in the areas of Internet infrastructure, system and network planning and administration, and software development with a focus on Internet infrastructure. This includes the design, deployment, audit, capacity planning, security and monitoring of enterprise class servers, services, and networks.
more...